Quantum computing is advancing faster than most organizations are prepared for—and its impact on today’s encryption standards could be profound. If you’re searching for clarity on how quantum breakthroughs threaten current security systems and what you can do about it, this article is designed to give you exactly that. We break down the real risks quantum machines pose to widely used cryptographic protocols, separate hype from reality, and explain the practical steps businesses and developers should be taking now.
You’ll also gain a clear understanding of post-quantum cryptography, how it works, and why transitioning early is critical for long-term data protection. Our insights are grounded in ongoing analysis of emerging research, security frameworks, and implementation strategies used across the tech industry. By the end, you’ll know what’s at risk, what’s changing, and how to future-proof your systems before quantum capabilities reach a tipping point.
The encryption protecting your bank logins and private messages relies on RSA and ECC. These systems depend on the difficulty of factoring large integers and solving discrete logarithms—tasks classical computers struggle with. Enter Shor’s algorithm. Running on a sufficiently powerful quantum computer, it can solve both problems efficiently, rendering today’s keys breakable. This isn’t science fiction; researchers have already demonstrated small-scale versions. To prepare, organizations should:
- audit cryptographic assets,
- prioritize crypto-agility (the ability to swap algorithms quickly),
- evaluate post-quantum cryptography standards now.
Waiting until machines mature means attackers could harvest encrypted data today and decrypt it tomorrow. Act early proactively.
An Introduction to Post-Quantum Cryptography (PQC)
As we navigate the rapidly evolving landscape of digital security with post-quantum cryptography, it’s essential to consider not only how we protect our data but also how the choice between native and cross-platform development can impact the implementation of these advanced security measures – for more details, check out our Native vs Cross-Platform Development: Which Approach Is Right?.
Post-quantum cryptography refers to classical encryption algorithms that run on today’s computers yet are designed to resist attacks from both classical and quantum machines. In other words, they don’t require futuristic hardware—just smarter math. This matters because researchers estimate that a sufficiently powerful quantum computer could break RSA and ECC using Shor’s algorithm, theoretically reducing security from billions of years to HOURS (National Institute of Standards and Technology, NIST).
To prepare, NIST launched a multi-year standardization project in 2016 to evaluate quantum-resistant algorithms. After reviewing 80+ submissions from global teams, NIST selected several finalists in 2022 for standardization, marking a MAJOR milestone in cybersecurity readiness.
The core principle is simple: rely on math problems believed to be hard for all computers. These include lattice-based systems (like CRYSTALS-Kyber), code-based schemes, hash-based signatures, and isogeny-based cryptography—each backed by peer-reviewed security analysis and ongoing public testing.
Deep Dive: Lattice-Based Cryptography – The New Standard
I still remember the first time I tried explaining lattice math to a room full of developers (blank stares, then nervous coffee sipping). That was before NIST selected CRYSTALS-Kyber for key encapsulation and CRYSTALS-Dilithium for digital signatures as primary standards. Today, they’re considered frontrunners in post-quantum cryptography because of their strong security proofs and impressive performance benchmarks (NIST, 2022).
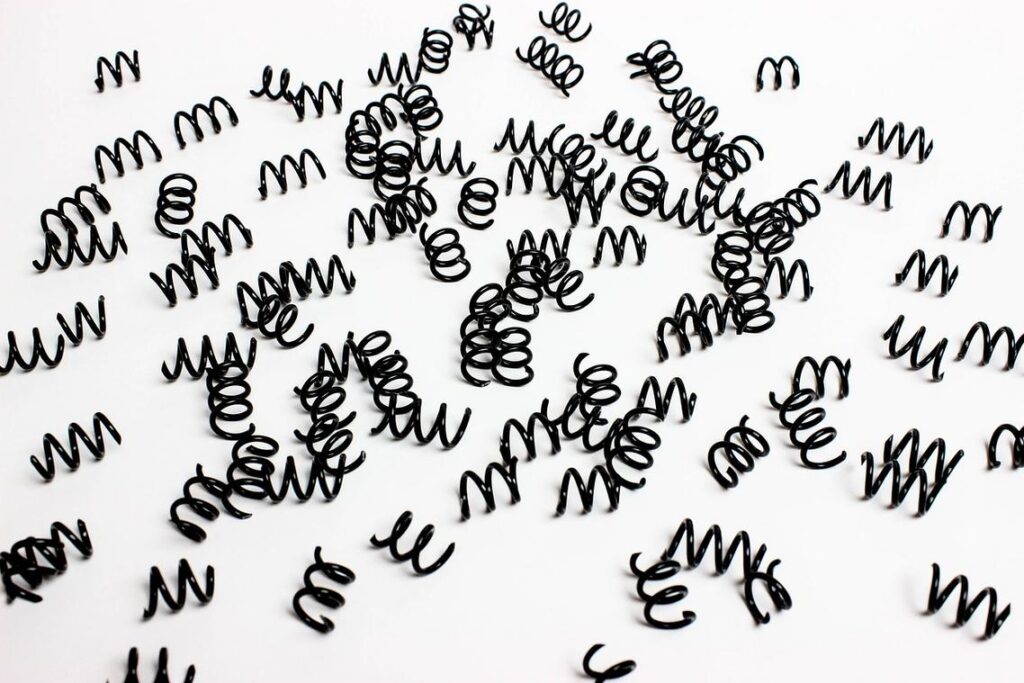
At the heart of lattice systems is the Shortest Vector Problem (SVP). A lattice is a grid of points extending in many dimensions. SVP asks: what’s the shortest non-zero line connecting two lattice points? Sounds simple—until you scale it to hundreds of dimensions. Imagine standing in a foggy mountain range trying to find the absolute shortest hiking path without seeing the terrain. That “closest point” becomes computationally infeasible to locate efficiently, even for quantum machines.
Some critics argue lattice keys are bulky compared to ECC. They’re right—key and signature sizes are larger. But in practice, developers gain:
- High efficiency
- Strong worst-case security reductions
When I first benchmarked Kyber in a test app, performance surprised me (in a good way). For teams worried about quantum attacks explained risks to financial systems and banks, the trade-off often feels worth it.
Exploring Other Key Quantum-Resistant Algorithm Families

Beyond lattice-based schemes, several other algorithm families are shaping the future of post-quantum cryptography. Each comes with distinct trade-offs that practitioners—especially those working in regulated sectors like fintech or defense—care deeply about.
First, Code-Based Cryptography relies on the hardness of decoding a random linear error-correcting code. In simple terms, an error-correcting code adds structured “noise” to data; reversing that noise without a secret key is computationally infeasible. Classic McEliece stands out here. It’s widely regarded as mature and battle-tested, with security roots dating back to 1978. The trade-off? Extremely large public keys—often hundreds of kilobytes—making integration tricky for bandwidth-constrained environments like IoT deployments.
Next, Hash-Based Signatures are built entirely on cryptographic hash functions—mathematical one-way functions that are easy to compute but nearly impossible to reverse. SPHINCS+ was standardized by NIST for digital signatures because of its conservative assumptions (no exotic math required). However, signatures are relatively large and verification can be slower—noticeable in high-throughput API gateways.
Finally, Multivariate Cryptography depends on the difficulty of solving systems of multivariate polynomial equations. It offers potentially fast signatures, attractive for embedded firmware updates, but remains mostly suited to specialized use cases (promising, yet still niche).
From Theory to Practice: The Hybrid Approach and Crypto-Agility
The hybrid model pairs a traditional algorithm like ECDH (Elliptic Curve Diffie-Hellman, a widely used key exchange method) with a PQC algorithm such as Kyber, a lattice-based key encapsulation mechanism selected by NIST. The benefit is simple but powerful: a connection remains secure as long as ONE of the two algorithms holds. Even if quantum attacks break ECDH, Kyber stands guard (think of it as having both a deadbolt and a biometric lock). This layered design is already being tested in TLS implementations to future-proof encrypted traffic.
Some critics argue hybrids add complexity and latency. That’s fair. Dual handshakes can increase packet size and processing time. However, benchmarks from NIST evaluations show optimized PQC libraries are becoming increasingly efficient, reducing performance trade-offs.
Crypto-agility means designing systems so algorithms can be swapped with minimal disruption. In an era of evolving standards and emerging flaws, this flexibility is CRITICAL. If vulnerabilities surface in post-quantum cryptography, agile systems can pivot quickly.
First steps:
1) Build a crypto-inventory of all public-key usage.
2) Test PQC libraries for performance impact.
3) Architect new systems with modular, REPLACEABLE cryptographic components.
Building a Quantum-Resistant Security Posture for Tomorrow
The transition away from vulnerable RSA and ECC algorithms is not optional—it’s inevitable. Quantum computers threaten to break widely used public-key systems through Shor’s algorithm, which can factor large integers exponentially faster than classical machines (NIST, 2022). The solution is clear: adopt NIST-approved standards and move toward post-quantum cryptography, with lattice-based schemes leading the charge due to their strong security proofs and performance balance.
Some argue large-scale quantum systems are still years away. That may be true. But “harvest now, decrypt later” attacks are already a risk—encrypted data stolen today could be cracked tomorrow.
Quantum resistance is not a one-time upgrade. It requires:
- Continuous cryptographic audits
- Testing hybrid key exchange models
- Monitoring NIST updates and threat intelligence
Pro tip: Stop deploying legacy cryptography in new systems immediately. Begin piloting hybrid PQC schemes in controlled environments now. The safest migration is the one started early.
Stay Ahead of the Quantum Disruption
You came here to understand how emerging technologies—especially quantum advancements—are reshaping security, machine learning, and modern app development. Now you have a clearer view of the risks, the opportunities, and why preparation can’t wait.
The reality is this: as quantum computing accelerates, traditional encryption methods will become vulnerable. That looming uncertainty is the pain point keeping tech leaders up at night. Ignoring it could mean data exposure, compliance failures, and lost trust. Acting early with post-quantum cryptography strategies and forward-thinking development practices is how you stay protected and competitive.
The smartest move you can make now is to stay consistently informed and implement quantum-ready security frameworks before threats materialize. Don’t wait for disruption to force your hand.
If you want real-time tech innovation alerts, actionable machine learning insights, and guidance on quantum-safe development strategies trusted by forward-thinking teams, subscribe now and stay ahead of the curve. The future is coming fast—make sure you’re ready for it.
 Ask James Danielsaylamans how they got into app development techniques and you'll probably get a longer answer than you expected. The short version: James started doing it, got genuinely hooked, and at some point realized they had accumulated enough hard-won knowledge that it would be a waste not to share it. So they started writing.
What makes James worth reading is that they skips the obvious stuff. Nobody needs another surface-level take on App Development Techniques, Emerging Tech Concepts and Trends, Machine Learning Insights. What readers actually want is the nuance — the part that only becomes clear after you've made a few mistakes and figured out why. That's the territory James operates in. The writing is direct, occasionally blunt, and always built around what's actually true rather than what sounds good in an article. They has little patience for filler, which means they's pieces tend to be denser with real information than the average post on the same subject.
James doesn't write to impress anyone. They writes because they has things to say that they genuinely thinks people should hear. That motivation — basic as it sounds — produces something noticeably different from content written for clicks or word count. Readers pick up on it. The comments on James's work tend to reflect that.
Ask James Danielsaylamans how they got into app development techniques and you'll probably get a longer answer than you expected. The short version: James started doing it, got genuinely hooked, and at some point realized they had accumulated enough hard-won knowledge that it would be a waste not to share it. So they started writing.
What makes James worth reading is that they skips the obvious stuff. Nobody needs another surface-level take on App Development Techniques, Emerging Tech Concepts and Trends, Machine Learning Insights. What readers actually want is the nuance — the part that only becomes clear after you've made a few mistakes and figured out why. That's the territory James operates in. The writing is direct, occasionally blunt, and always built around what's actually true rather than what sounds good in an article. They has little patience for filler, which means they's pieces tend to be denser with real information than the average post on the same subject.
James doesn't write to impress anyone. They writes because they has things to say that they genuinely thinks people should hear. That motivation — basic as it sounds — produces something noticeably different from content written for clicks or word count. Readers pick up on it. The comments on James's work tend to reflect that.