Quantum computing is advancing faster than most security frameworks can keep up—and that has serious implications for anyone relying on today’s encryption standards. If you’re searching for clarity on how quantum breakthroughs could expose sensitive data, disrupt digital infrastructure, and reshape cybersecurity strategy, this article is built for you. We break down the real-world risks emerging from quantum computing threats, explain what industries are most vulnerable, and outline practical steps toward quantum security mitigation before large-scale quantum systems become mainstream.
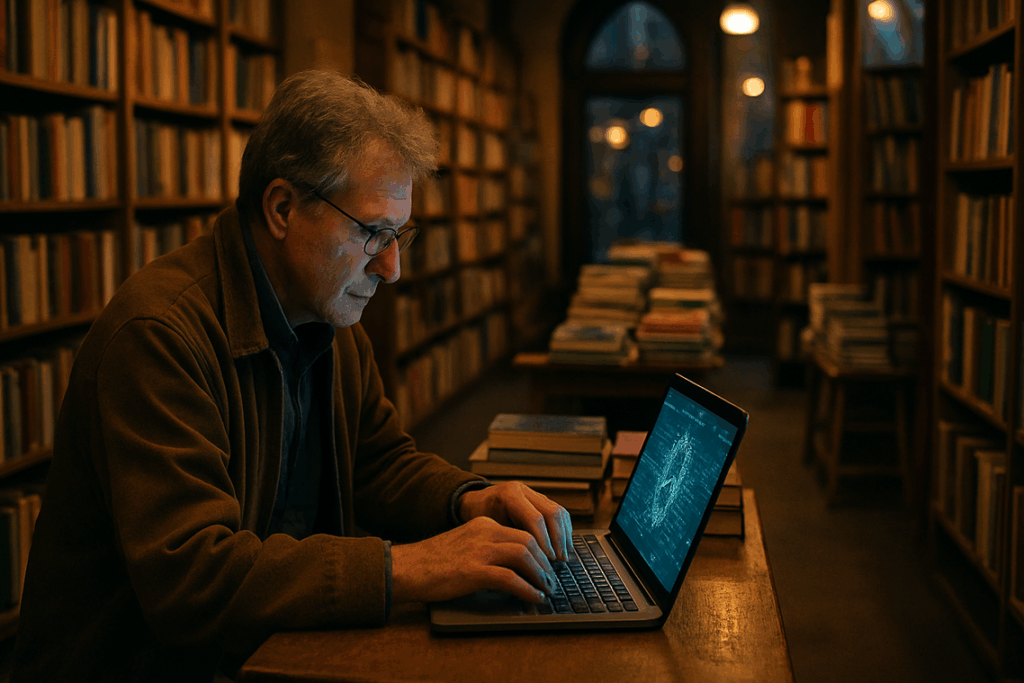
Our insights are grounded in ongoing analysis of peer-reviewed research, emerging tech briefings, and direct evaluations of current cryptographic transition efforts. Rather than speculation, you’ll find evidence-based guidance on machine learning’s role in threat detection, evolving encryption models, and the proactive strategies organizations are adopting right now. By the end, you’ll understand not just the risks—but the concrete actions needed to stay ahead in the quantum era.
The countdown to “Q-Day” isn’t science fiction; it’s a slow, measurable shift in computing power. Today’s RSA and ECC encryption feel unbreakable, yet they rely on math problems quantum machines are designed to solve. Early in my career, I dismissed this as hype. After all, practical quantum computers seemed decades away. However, I overlooked harvest-now, decrypt-later attacks, where adversaries store encrypted data until breakthroughs arrive. That mistake changed my approach. Instead of waiting, we began inventorying sensitive assets and prioritizing systems with long confidentiality lifespans. Next, we tested post-quantum algorithms recommended by NIST, integrating them alongside existing controls. This layered quantum security mitigation strategy reduced future exposure. Still, skeptics argue large-scale quantum machines may stall. Perhaps. But cryptographic migrations take years, not months; delay risks.
Shattering the Foundation: How Quantum Computers Break Today’s Cryptography
The Core Vulnerability
Classical computers use bits—tiny switches that are either 0s or 1s. Quantum computers use qubits, which can exist as 0, 1, or both at once through superposition. That difference sounds subtle, but it changes everything. I once dismissed this as lab hype (a sci‑fi subplot at best), and that was my first mistake. Qubits also leverage entanglement, meaning their states become linked in ways classical bits never could.
Shor’s Algorithm Explained
Most public-key cryptography relies on the difficulty of factoring large numbers. Multiply two huge primes, and classical machines struggle to reverse the product. Shor’s algorithm exploits quantum parallelism to factor those numbers efficiently. What would take classical systems billions of years could shrink dramatically. I learned the hard way that “hard” in math does not mean “forever.”
What’s at Risk?
TLS/SSL sessions, digital signatures, cryptocurrency wallets, and long-term archives all depend on that math. The looming “Harvest Now, Decrypt Later” strategy means adversaries can store encrypted traffic today and unlock it tomorrow. The lesson is clear: delaying quantum security mitigation planning repeats my early complacency. Act before the foundation cracks. Right now, prepare wisely.
Introducing Post-Quantum Cryptography (PQC): The New Digital Shield

Post-Quantum Cryptography (PQC) refers to a new generation of encryption algorithms designed to resist attacks from both classical computers (today’s machines) and future quantum computers. If you’ve read about how quantum computing could break traditional encryption (https://rcsdassk.com.co/how-quantum-computing-could-break-traditional-encryption), you already know why this shift matters.
How PQC Works (Without the Math Headache)
Instead of relying on factoring large numbers (like RSA does), PQC is built on tougher mathematical puzzles, including:
- Lattice-based cryptography – relies on complex geometric structures that are extremely hard to solve.
- Code-based cryptography – built around error-correcting codes.
- Hash-based cryptography – strengthens digital signatures using secure hash functions.
These problems are believed to resist quantum attacks—even those powered by Shor’s algorithm (the quantum equivalent of a lock-picking master).
NIST’s Role: Order in the Chaos
The National Institute of Standards and Technology (NIST) has led a multi-year competition to standardize PQC algorithms. Winners like CRYSTALS-Kyber (for encryption) and CRYSTALS-Dilithium (for digital signatures) provide a clear migration path forward.
PQC vs. Quantum Cryptography: Not the Same Thing
- PQC = Software upgrade. New algorithms, same infrastructure.
- Quantum Key Distribution (QKD) = Hardware-based system using quantum physics.
Think of PQC as updating your operating system, while QKD is rewiring the entire house. For scalable quantum security mitigation, most organizations are prioritizing PQC first (pro tip: start hybrid deployments early).
Your 4-Step Quantum Readiness Playbook
Quantum threats aren’t theoretical anymore. Since NIST began standardizing post-quantum cryptography (PQC) algorithms in 2016—and announced its first selections in 2022—organizations have had nearly a decade of warning. The clock isn’t ticking loudly yet, but it is ticking.
Step 1: Cryptographic Inventory & Discovery
You can’t protect what you can’t see. Start by identifying every instance of public-key cryptography (encryption that uses a public and private key pair) across:
- Applications
- Network devices
- Cloud workloads
- Embedded systems
This includes TLS certificates, VPNs, code-signing tools, and even forgotten legacy servers (yes, those). After three months of audits, many enterprises discover shadow IT systems still using RSA-2048.
Step 2: Risk Assessment & Prioritization
Not all systems deserve equal urgency. Ask:
- Which systems protect sensitive or regulated data?
- Which data must remain secure for 10+ years?
- Where would decryption cause irreversible harm?
Long-lived data—like health records or intellectual property—is most vulnerable to “harvest now, decrypt later” attacks. Prioritize accordingly.
Step 3: Testing & Integration
PQC keys are often larger and computationally heavier than classical algorithms. In controlled test environments, measure latency, bandwidth impact, and compatibility. Some teams report performance dips of 5–15% during early pilots. That’s manageable—but only if you plan for it.
Step 4: Phased Migration & Crypto-Agility
This isn’t a flip-the-switch moment. Begin with high-priority systems, then expand gradually. Build for crypto-agility—the ability to swap algorithms without redesigning infrastructure. True quantum security mitigation depends on systems that adapt as standards evolve over the next decade.
From Threat to Action
Last year, I sat in a boardroom where our security team insisted quantum attacks were decades away. It felt comforting—until it wasn’t. When we mapped our encrypted backups, we realized sensitive client data could be harvested now and decrypted later.
That’s the real risk. Not sci-fi, but “harvest now, decrypt later.” Think of it like recording a locked safe combination for future tech to crack.
Start with:
- Inventory your cryptographic assets.
- Assess exposure to vulnerable algorithms.
- Plan phased quantum security mitigation.
Pro tip: assign ownership early. The first move is a candid internal conversation today. Seriously.
As we explore these mitigation strategies for quantum-era data security, it’s essential to also consider how staying ahead of disruptive tech innovations can help organizations adapt and enhance their security frameworks before they become a pressing concern – for more details, check out our How to Track Disruptive Tech Innovations Before They Go Mainstream.
Stay Ahead of the Next Wave of Tech Disruption
You came here to understand where emerging technology is headed — from machine learning breakthroughs to the real risks posed by quantum computing. Now you have a clearer view of the trends shaping innovation and the vulnerabilities that could impact your systems, data, and competitive edge.
The reality is simple: technology is evolving faster than most teams can adapt. Falling behind on AI advancements, ignoring quantum-era threats, or overlooking secure app development practices can expose you to costly setbacks. The pain point isn’t lack of opportunity — it’s lack of timely, actionable insight.
That’s why staying proactive matters. Prioritizing quantum security mitigation strategies, tracking emerging tech signals, and refining your development approach today will protect your infrastructure tomorrow.
If you’re serious about staying competitive, don’t wait for disruption to force your hand. Get real-time tech innovation alerts, practical machine learning insights, and forward-looking security guidance trusted by forward-thinking professionals. Start implementing smarter strategies now and position yourself ahead of the curve before the next wave hits.

 Norman Liaoctoreno is the kind of writer who genuinely cannot publish something without checking it twice. Maybe three times. They came to app development techniques through years of hands-on work rather than theory, which means the things they writes about — App Development Techniques, Emerging Tech Concepts and Trends, Machine Learning Insights, among other areas — are things they has actually tested, questioned, and revised opinions on more than once.
That shows in the work. Norman's pieces tend to go a level deeper than most. Not in a way that becomes unreadable, but in a way that makes you realize you'd been missing something important. They has a habit of finding the detail that everybody else glosses over and making it the center of the story — which sounds simple, but takes a rare combination of curiosity and patience to pull off consistently. The writing never feels rushed. It feels like someone who sat with the subject long enough to actually understand it.
Outside of specific topics, what Norman cares about most is whether the reader walks away with something useful. Not impressed. Not entertained. Useful. That's a harder bar to clear than it sounds, and they clears it more often than not — which is why readers tend to remember Norman's articles long after they've forgotten the headline.
Norman Liaoctoreno is the kind of writer who genuinely cannot publish something without checking it twice. Maybe three times. They came to app development techniques through years of hands-on work rather than theory, which means the things they writes about — App Development Techniques, Emerging Tech Concepts and Trends, Machine Learning Insights, among other areas — are things they has actually tested, questioned, and revised opinions on more than once.
That shows in the work. Norman's pieces tend to go a level deeper than most. Not in a way that becomes unreadable, but in a way that makes you realize you'd been missing something important. They has a habit of finding the detail that everybody else glosses over and making it the center of the story — which sounds simple, but takes a rare combination of curiosity and patience to pull off consistently. The writing never feels rushed. It feels like someone who sat with the subject long enough to actually understand it.
Outside of specific topics, what Norman cares about most is whether the reader walks away with something useful. Not impressed. Not entertained. Useful. That's a harder bar to clear than it sounds, and they clears it more often than not — which is why readers tend to remember Norman's articles long after they've forgotten the headline.